Pentesterra DevGuard — VS Code Security Extension

Pre-push security audit for your codebase.
DevGuard analyzes dependencies, secrets metadata, misconfigurations, AI toolchain risks, crypto weaknesses, and other security signals directly from your IDE before code reaches production.
Compatible with:
Key Features
- Pre-push security gate that blocks vulnerable commits
- Dependency vulnerability analysis across 15 ecosystems
- Secrets metadata detection (without transmitting secrets)
- Misconfiguration and crypto misuse detection
- AI supply-chain risk analysis
- Attack Vectors — code-to-impact path analysis
- Risk scoring with severity classification
- Native IDE workflow — no CI setup required
Supported IDEs
DevGuard works with:
Supported Ecosystems (15 Parsers)
| Ecosystem |
Lockfile / Manifest |
| npm |
package-lock.json, yarn.lock, pnpm-lock.yaml |
| Python |
requirements.txt, Pipfile.lock, poetry.lock |
| Go |
go.sum |
| Rust |
Cargo.lock |
| Ruby |
Gemfile.lock |
| PHP |
composer.lock |
| Java / Kotlin |
pom.xml, build.gradle, build.gradle.kts |
| .NET / NuGet |
packages.lock.json |
| Swift |
Package.resolved |
| Dart / Flutter |
pubspec.lock |
Installation
Install from VS Code Marketplace:
https://marketplace.visualstudio.com/items?itemName=pentesterra.pentesterra-devguard
Or install locally:
code --install-extension pentesterra-devguard-1.1.2.vsix
Cursor:
cursor --install-extension pentesterra-devguard-1.1.2.vsix
Windsurf:
windsurf --install-extension pentesterra-devguard-1.1.2.vsix
Antigravity:
antigravity --install-extension pentesterra-devguard-1.1.2.vsix
Prerequisites
DevGuard CLI
Install the CLI collector:
pip install pentesterra-devguard
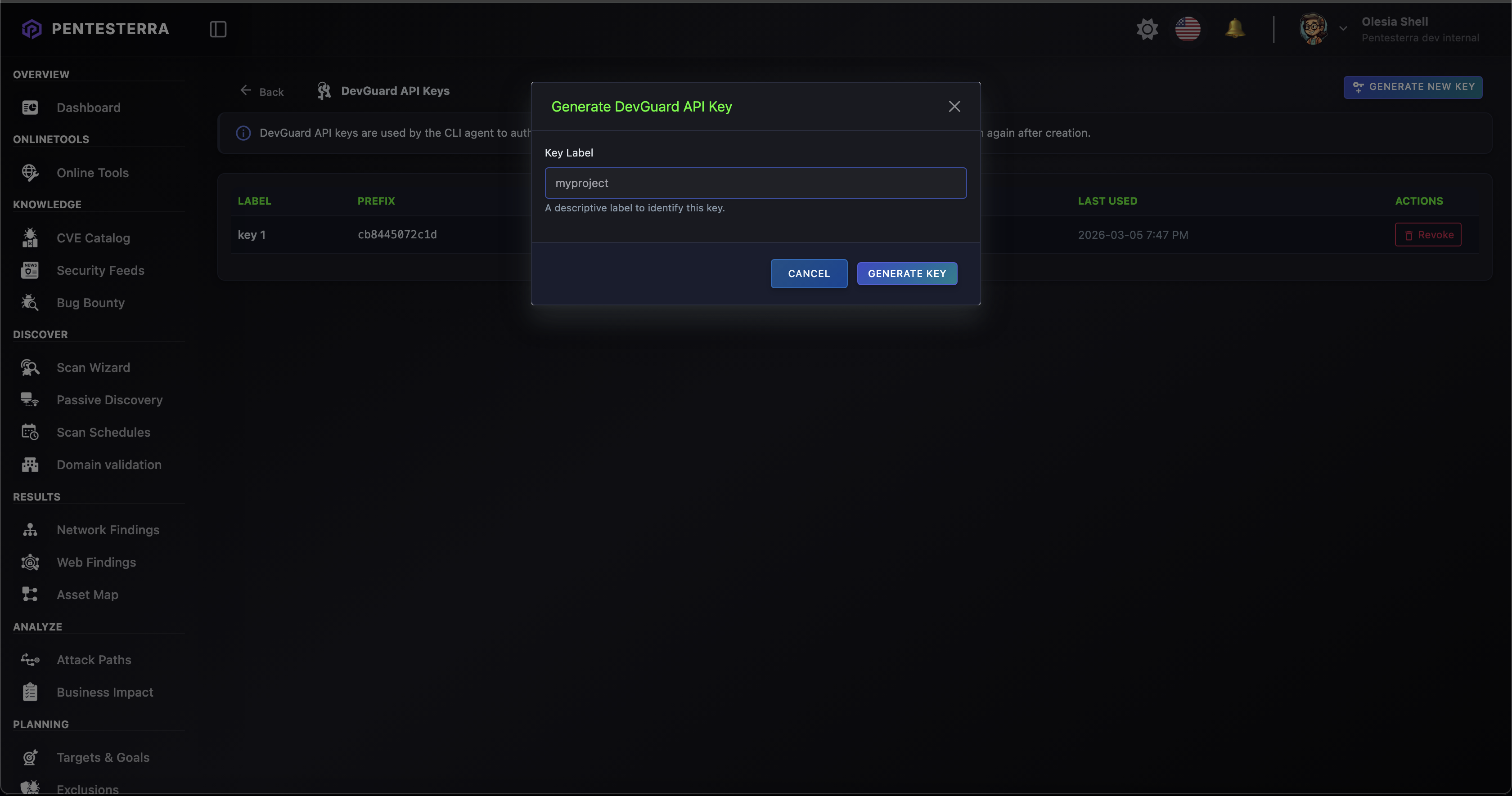
API Key
Generate an API key from:
https://app.pentesterra.com → DevGuard → API Keys
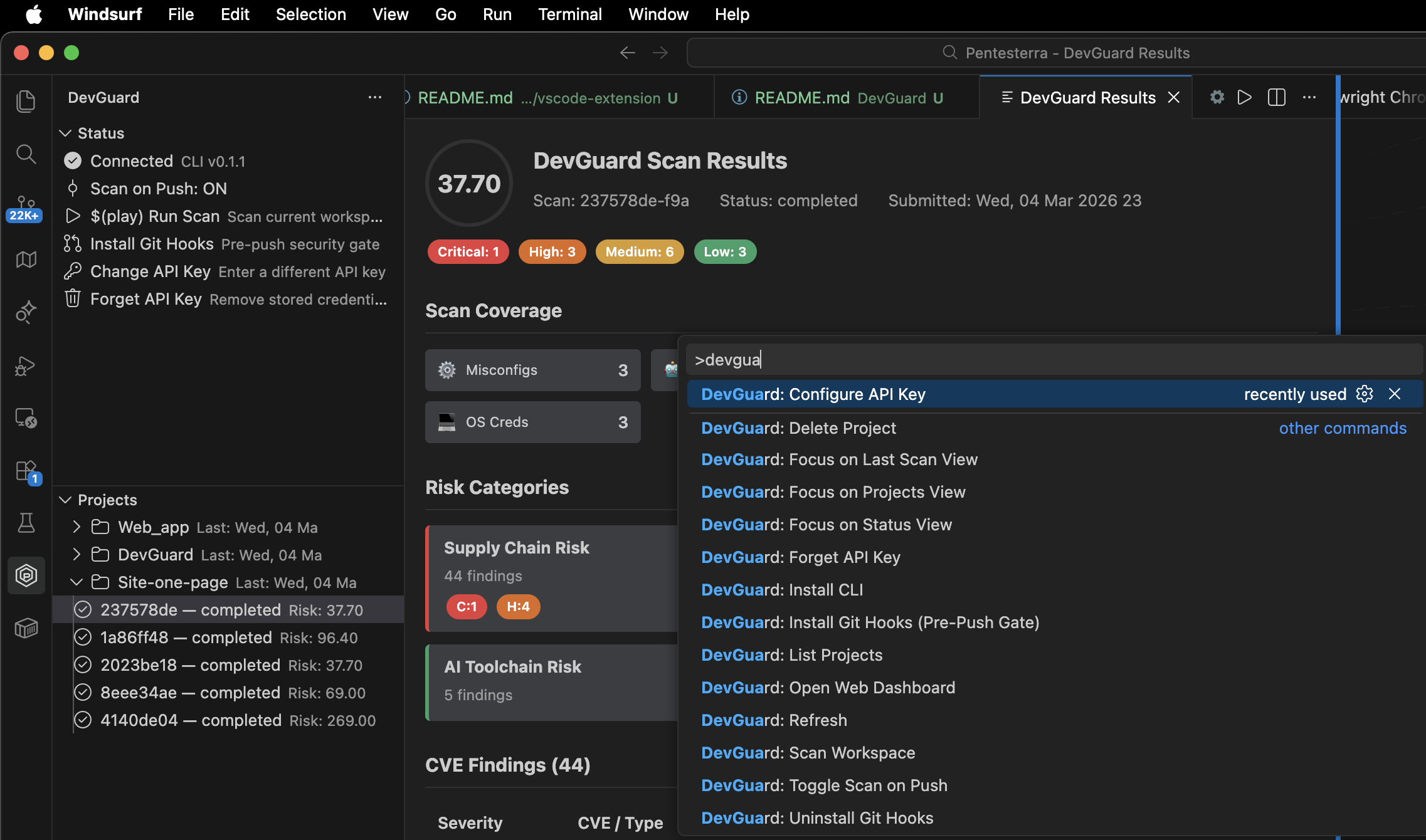
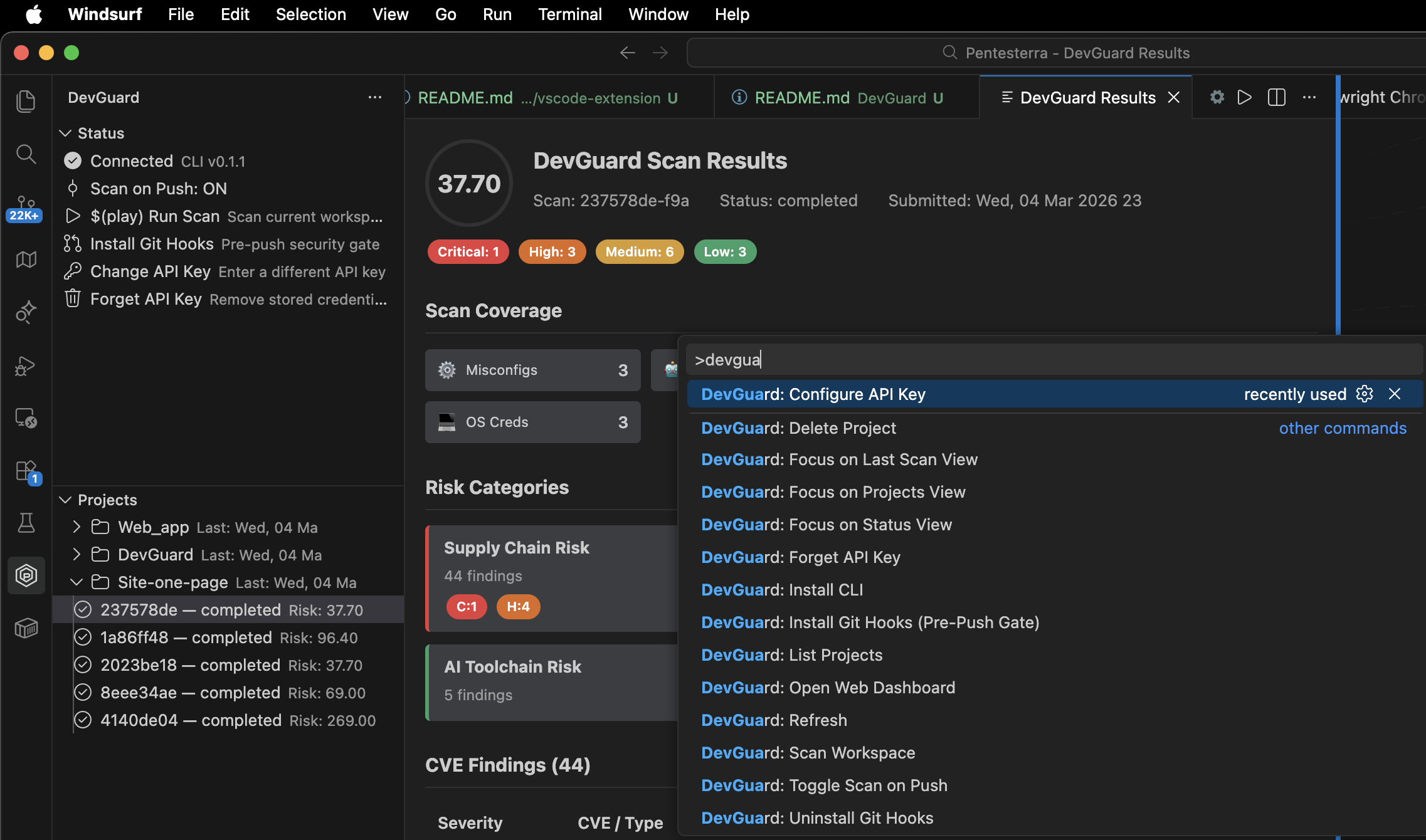
Quick Start
- Open Command Palette
- Run DevGuard: Configure API Key
- Enter your
dg_... API key
- Run DevGuard: Scan Workspace
You can also trigger scans via the DevGuard sidebar.
Features
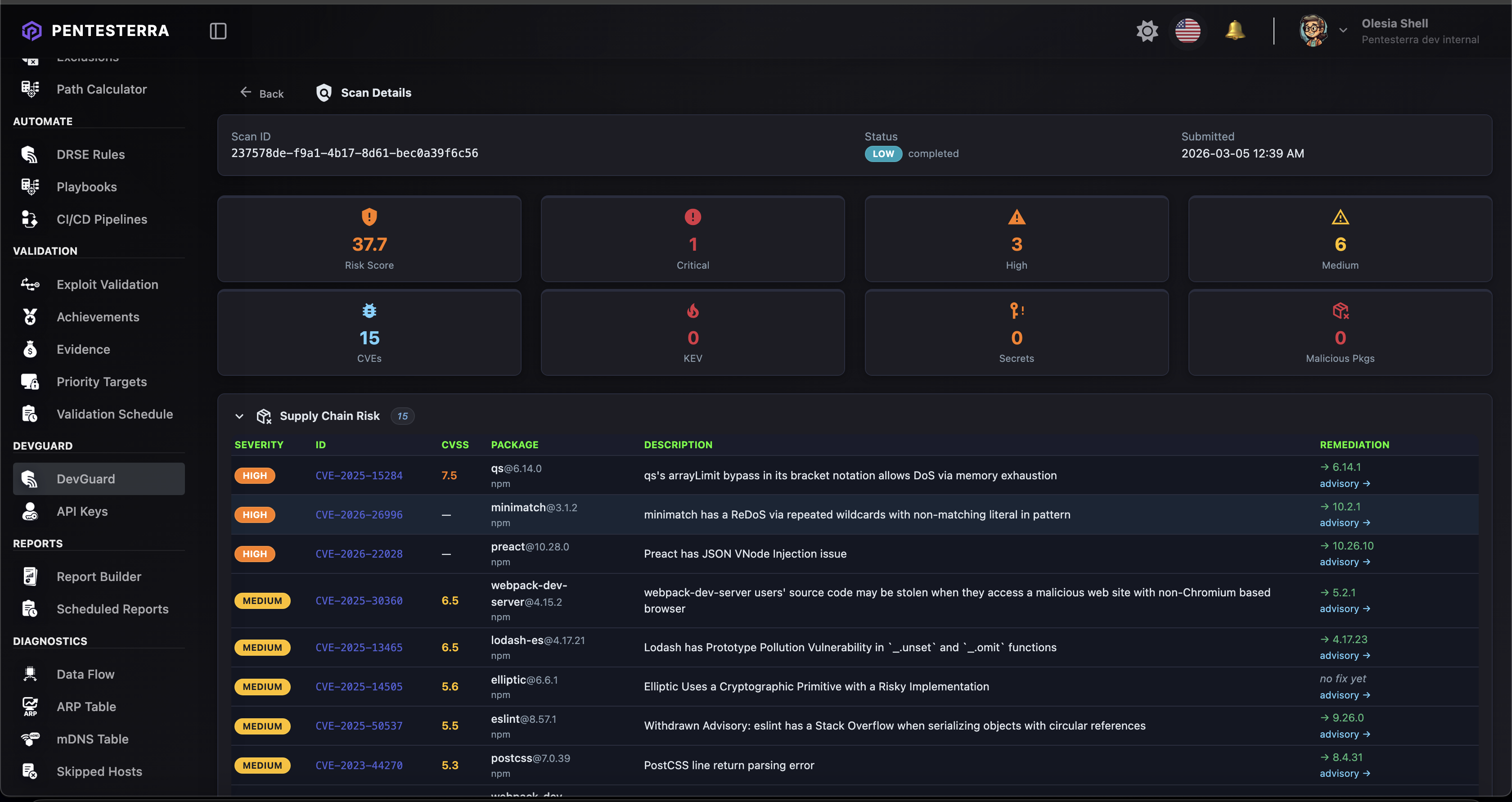
Scan Workspace
Collects security signals from your project:
- dependency metadata
- secrets metadata
- configuration risks
- cryptographic misuse
- supply-chain signals
Data is analyzed via the Pentesterra API using a three-stage analysis pipeline:
- CPE matching
- advisory correlation
- LLM fallback analysis
Pre-Push Security Gate
DevGuard can install a real git pre-push hook that blocks pushes when vulnerabilities exceed a defined severity threshold.
Install from Command Palette:
DevGuard: Install Git Hooks (Pre-Push Gate)
Available thresholds:
critical
high
medium
none
Push can be bypassed with:
git push --no-verify
Scan on Push (Telemetry Mode)
DevGuard can automatically scan your workspace after every git push.
This mode does not block pushes and is useful for telemetry and continuous monitoring.
Toggle via:
DevGuard: Toggle Scan on Push
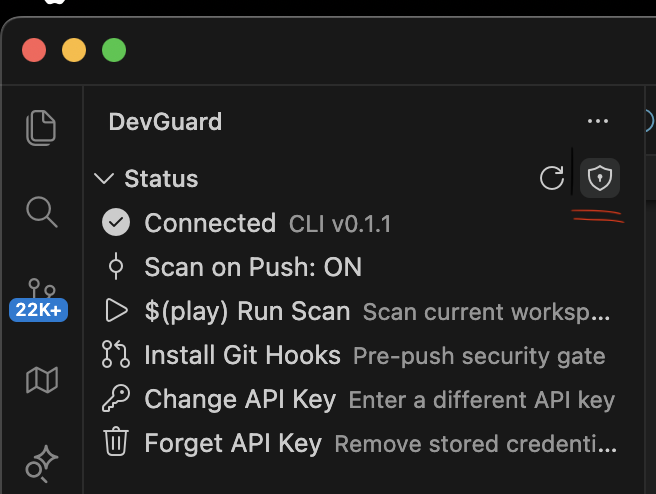
Access DevGuard via the Activity Bar.
Panels include:
Status
Connection status, CLI version, scan configuration.
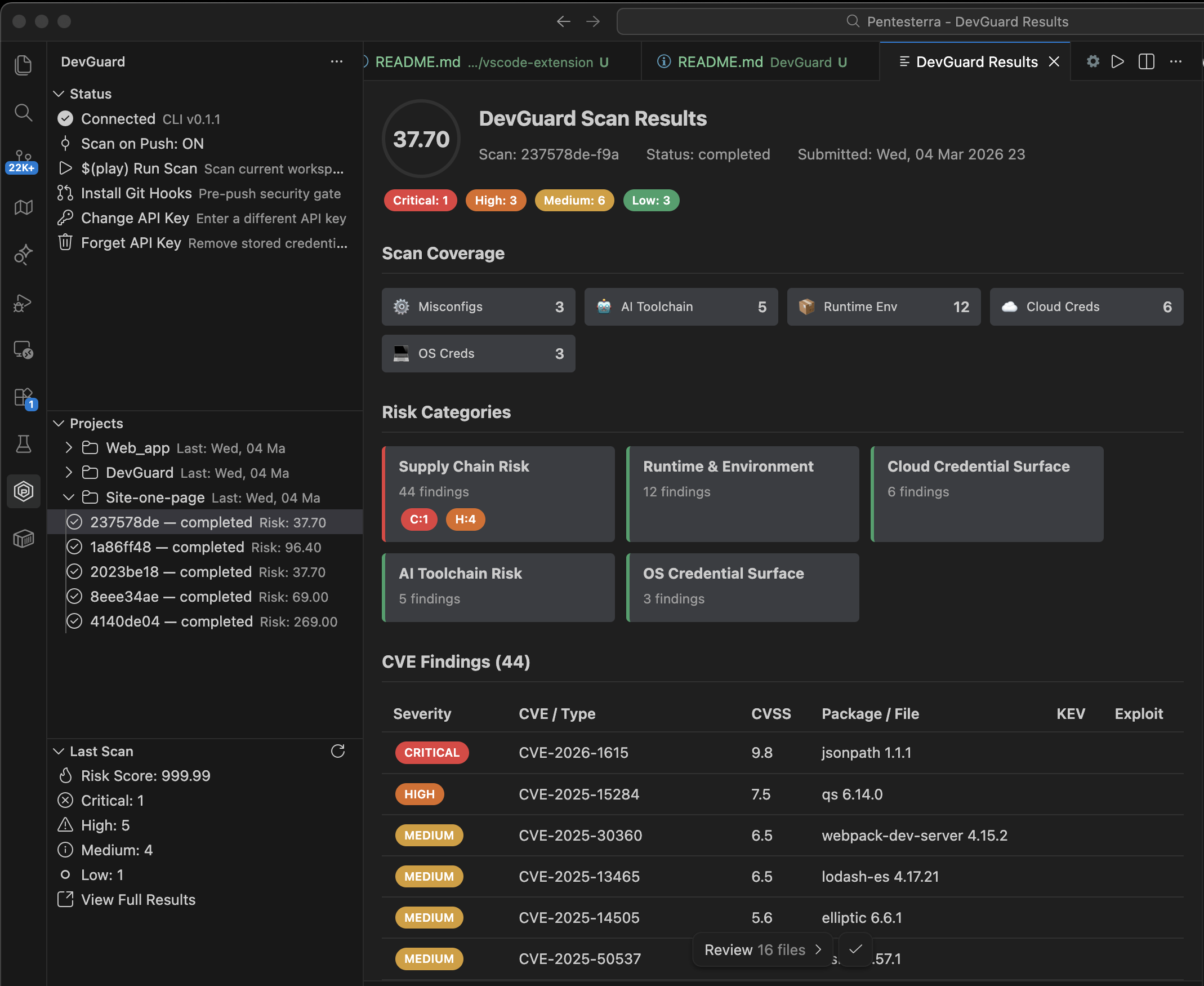
Projects
Your DevGuard projects with recent scan history.
Last Scan
Risk score and severity summary.
Git Hooks
Install or remove the pre-push security gate.
Credentials
Remove stored API key.
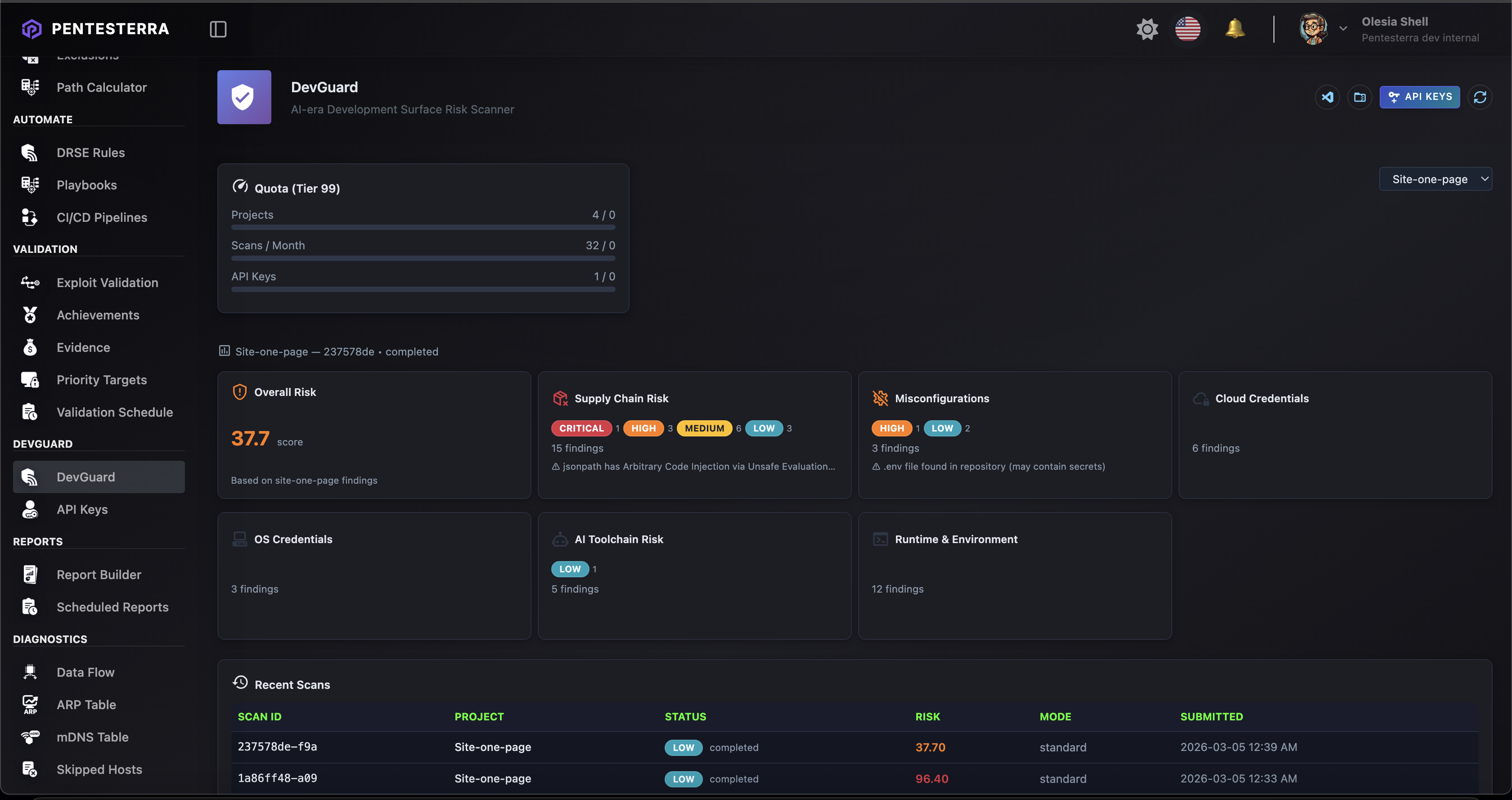
Results Webview
DevGuard provides a rich HTML results panel including:
- risk score gauge
- severity badges
- risk category cards
- findings table
- attack vectors analysis (code-to-impact paths)
The interface automatically adapts to light and dark themes.
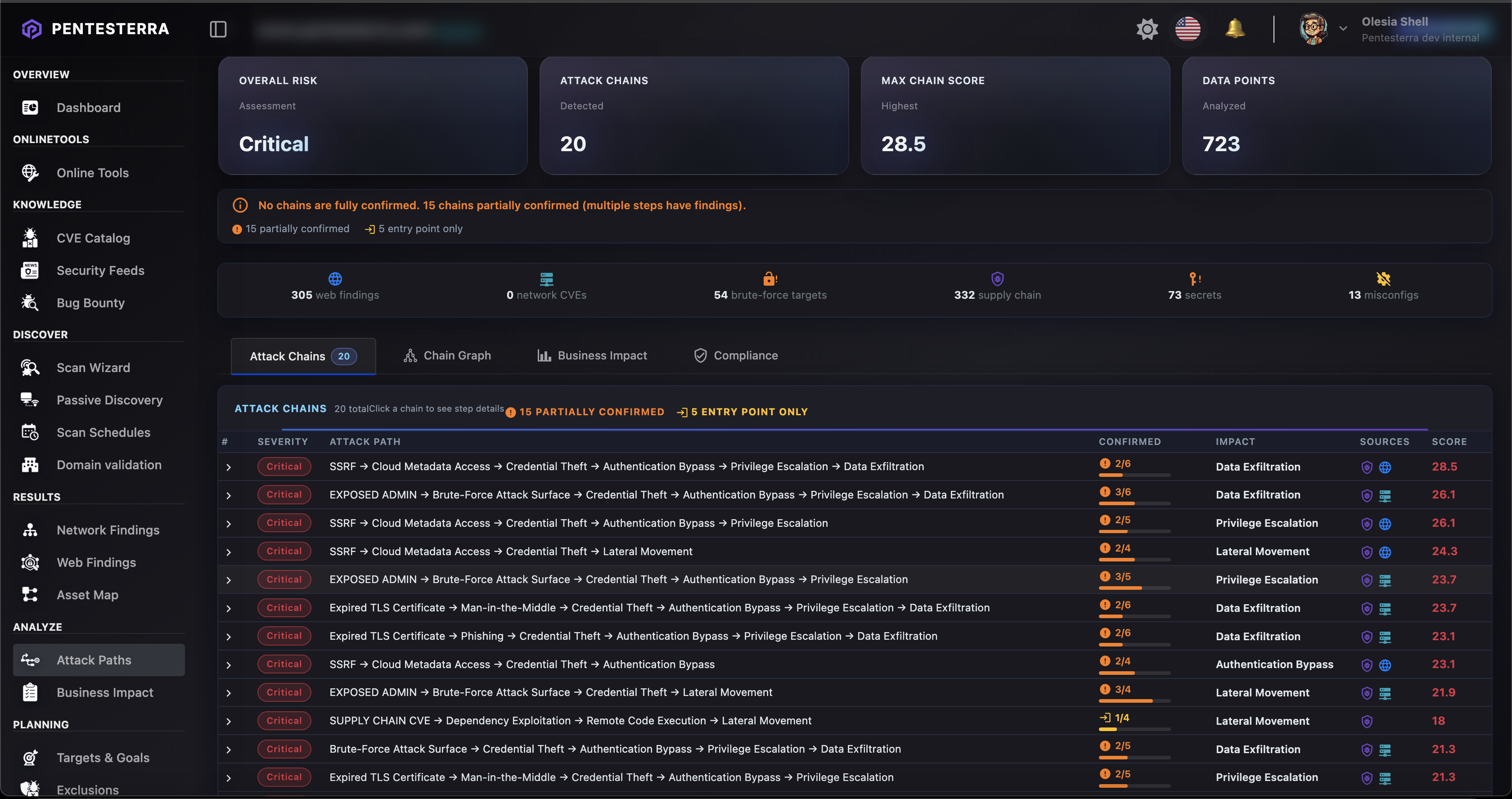
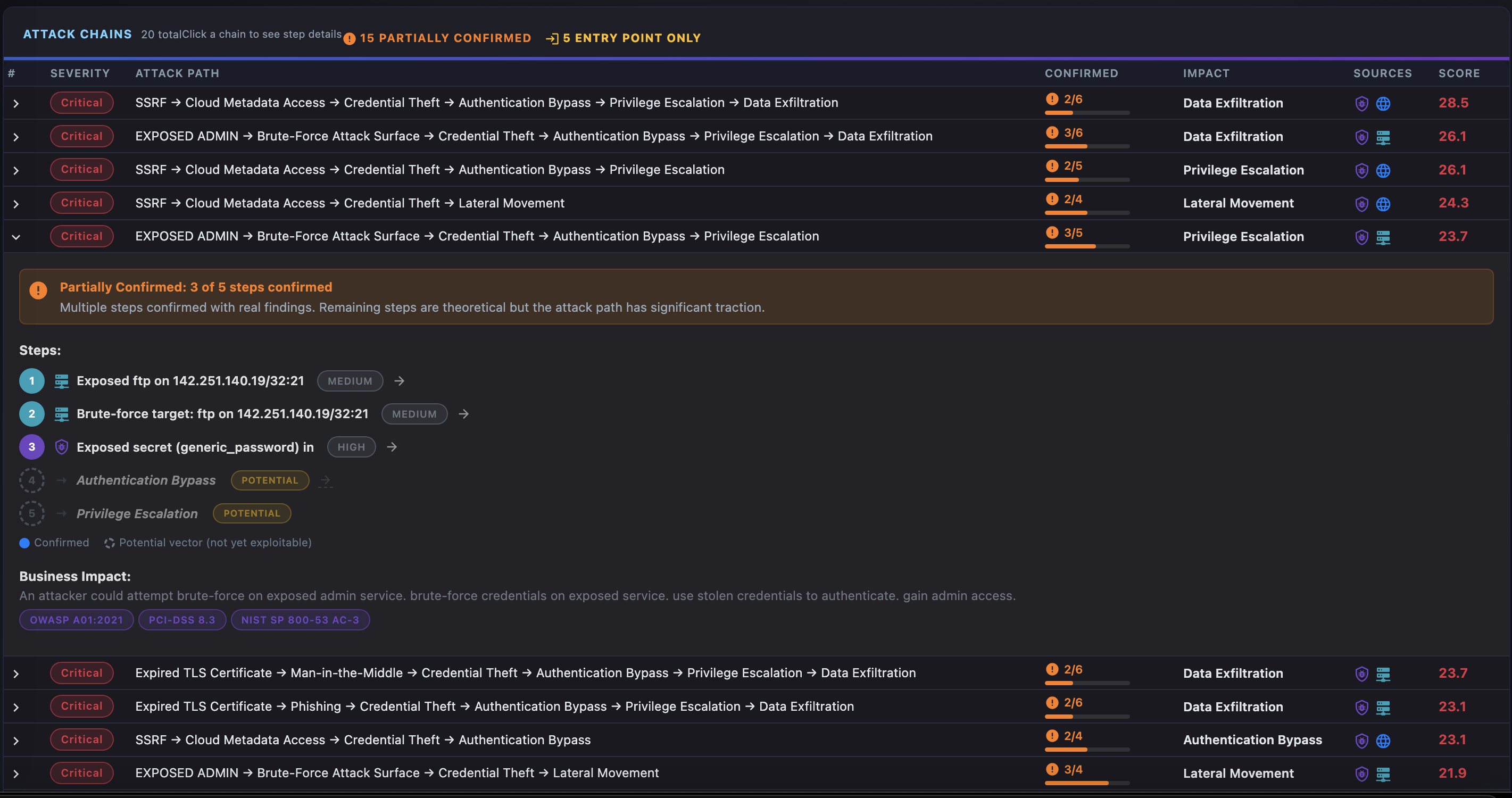
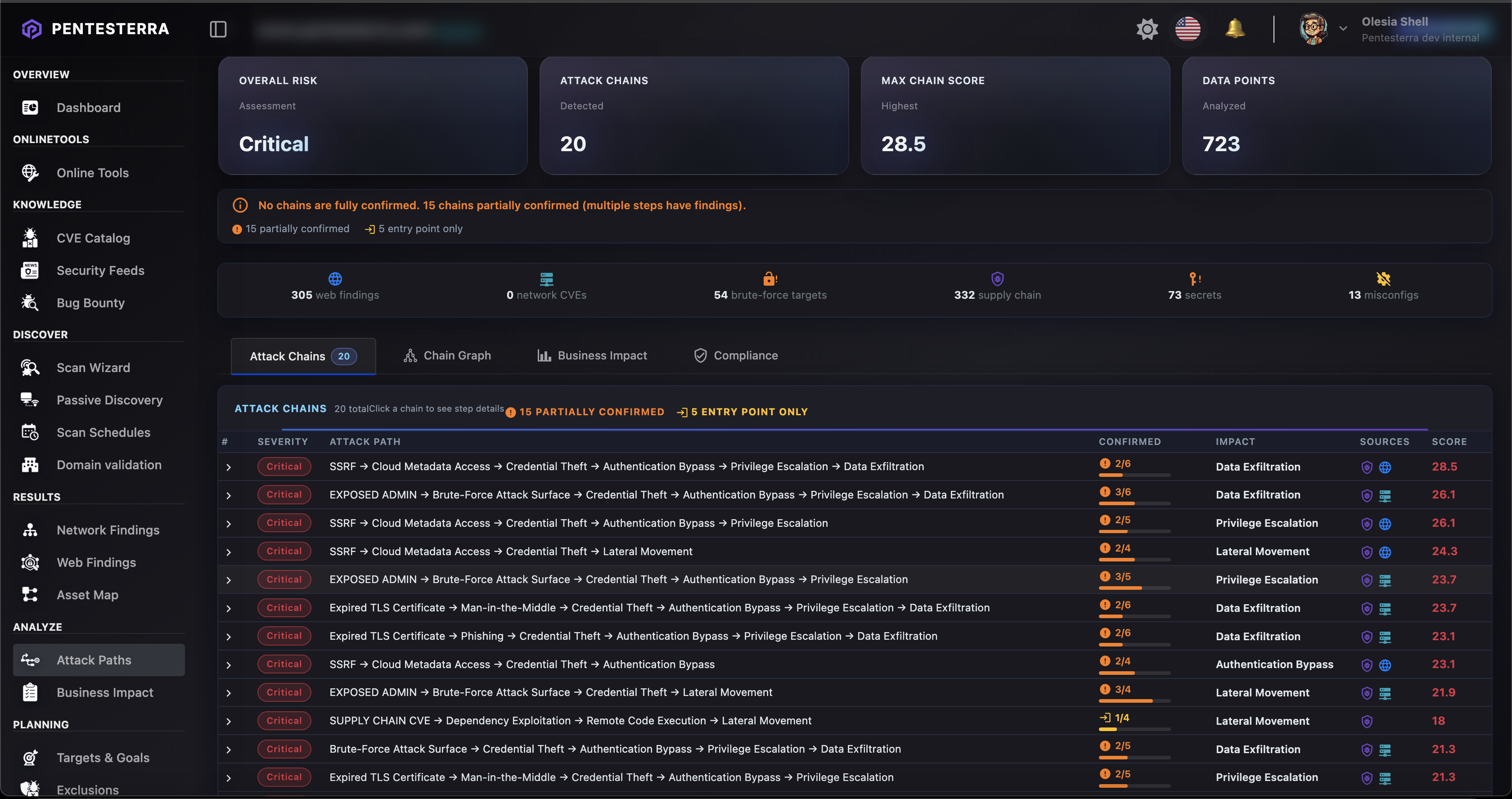
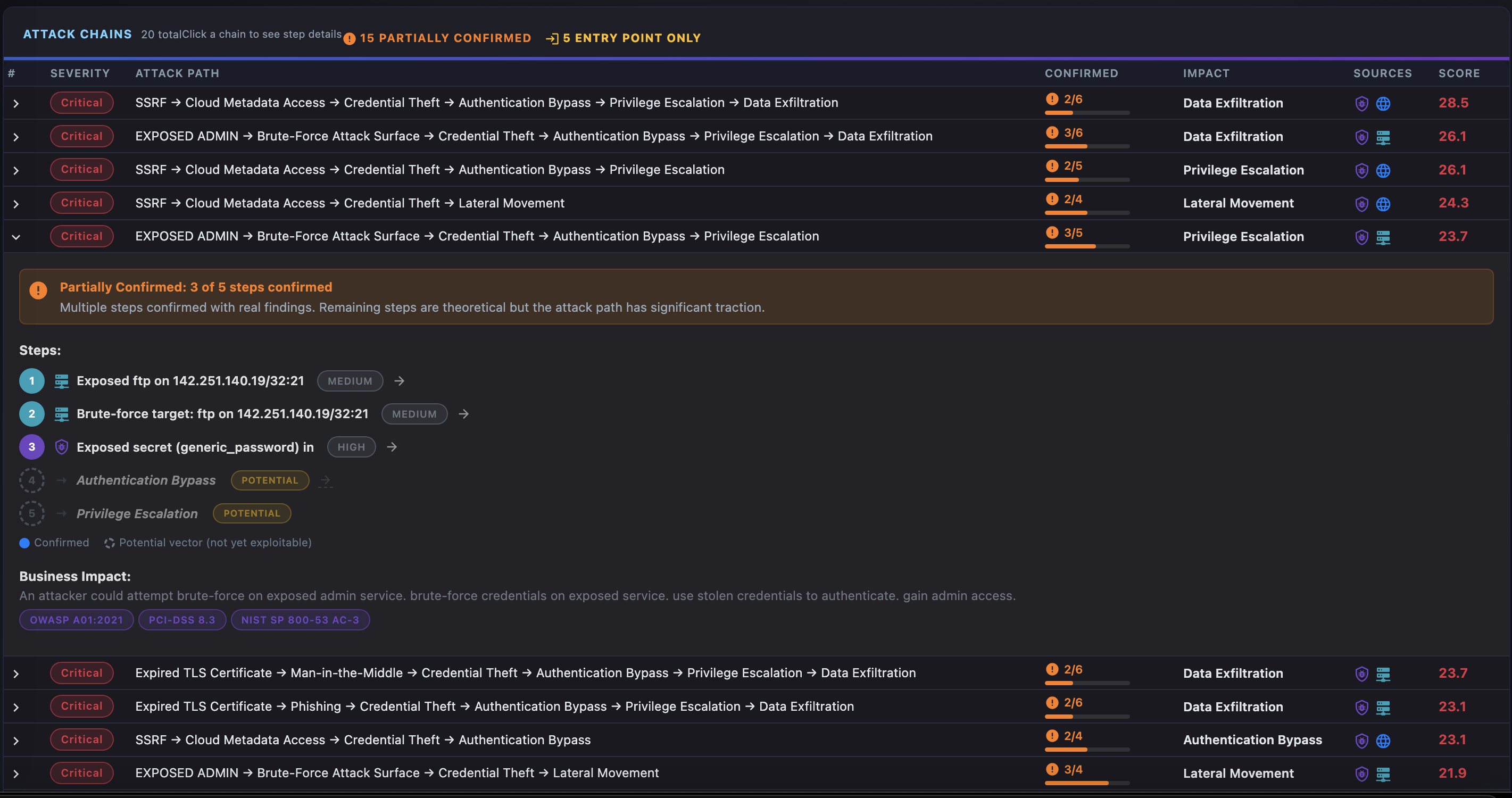
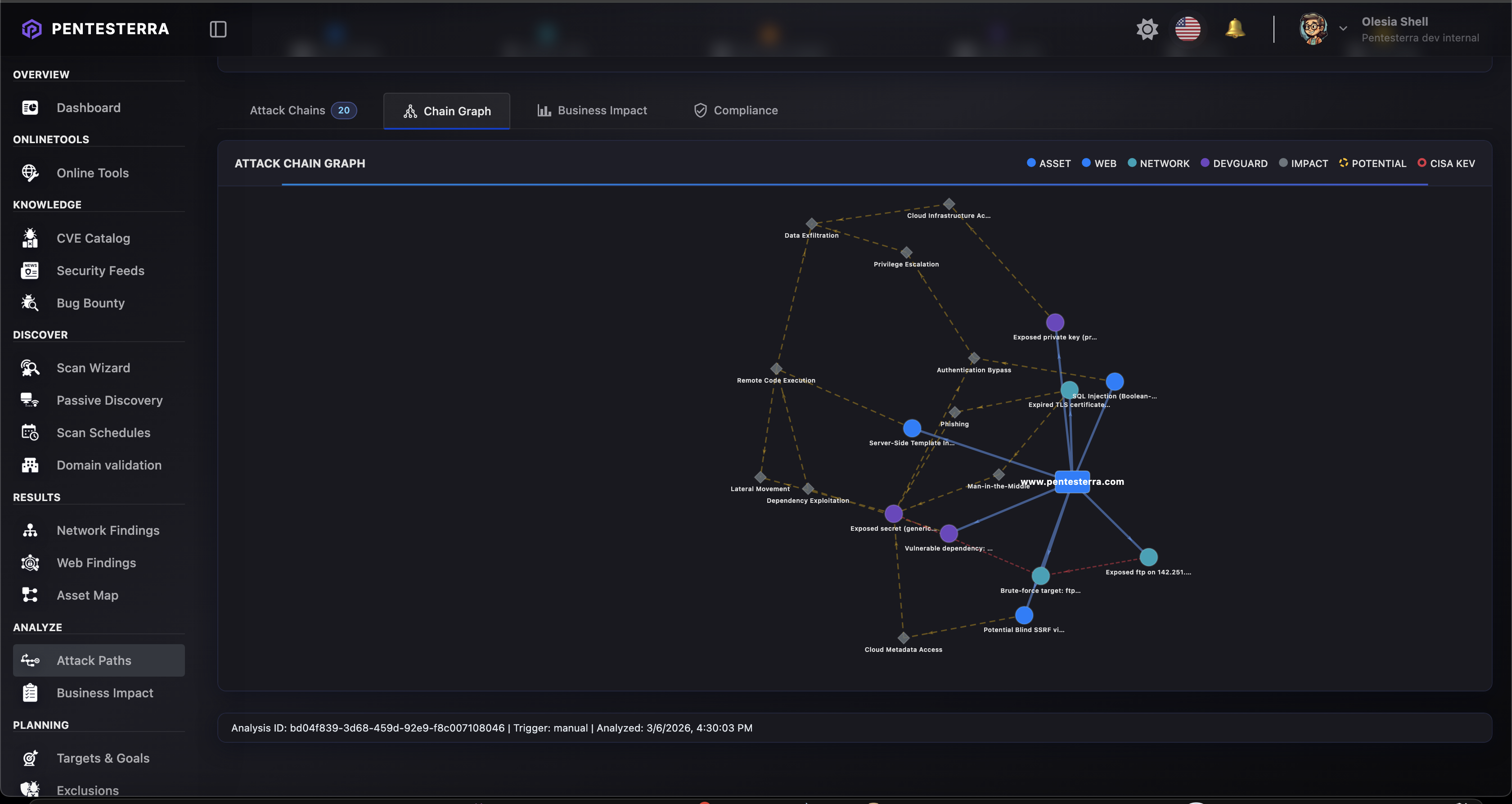
Attack Vectors Analysis
DevGuard automatically generates Attack Vectors — code-to-impact paths based on your security findings.
Attack Vectors show how vulnerabilities, secrets, and misconfigurations can chain together to create exploitable attack paths.
What are Attack Vectors?
Unlike traditional Attack Chains (which require offensive testing), DevGuard Attack Vectors are potential paths identified through static analysis:
- Code-to-Impact Paths: From exposed secrets → service access → privilege escalation
- Dependency Chains: From vulnerable dependency → reachable code → RCE potential
- CI/CD Vectors: From CI/CD secrets → repository access → supply chain compromise
- Crypto Weaknesses: From weak crypto → offline attack → credential theft
Viewing Attack Vectors
Attack Vectors appear in:
- IDE Command — Run
DevGuard: Analyze Attack Vectors from Command Palette
- Results Webview — Top 5 chains displayed with severity and evidence level
- Web Dashboard — Full analysis at
https://app.pentesterra.com/#/attackchains
- CLI —
pentesterra-devguard attack-vectors command
Triggering Analysis
You can trigger Attack Vectors analysis directly from your IDE:
- Open Command Palette (
Cmd+Shift+P / Ctrl+Shift+P)
- Run DevGuard: Analyze Attack Vectors
- Wait for analysis to complete
- Choose to view in Dashboard or Results Panel
The analysis uses your latest DevGuard scan data to generate code-to-impact paths.
Evidence Levels
Each attack vector has a confirmation level:
- 🔗 Evidence-backed — Multiple DevGuard findings support the path
- 📦 Dependency-confirmed — CVE + reachable import context
- 🔑 Secret-backed — Exposed secret + service context
- 💭 Theoretical — Potential path requiring validation
Example Attack Vector
CRITICAL (Score: 9.2) — 🔗 Evidence-backed
exposed_secret_cloud → service_access → privilege_escalation → data_exfiltration
Impact: Unauthorized access to production cloud infrastructure
Attack Vectors help prioritize remediation by showing real-world impact of individual findings.
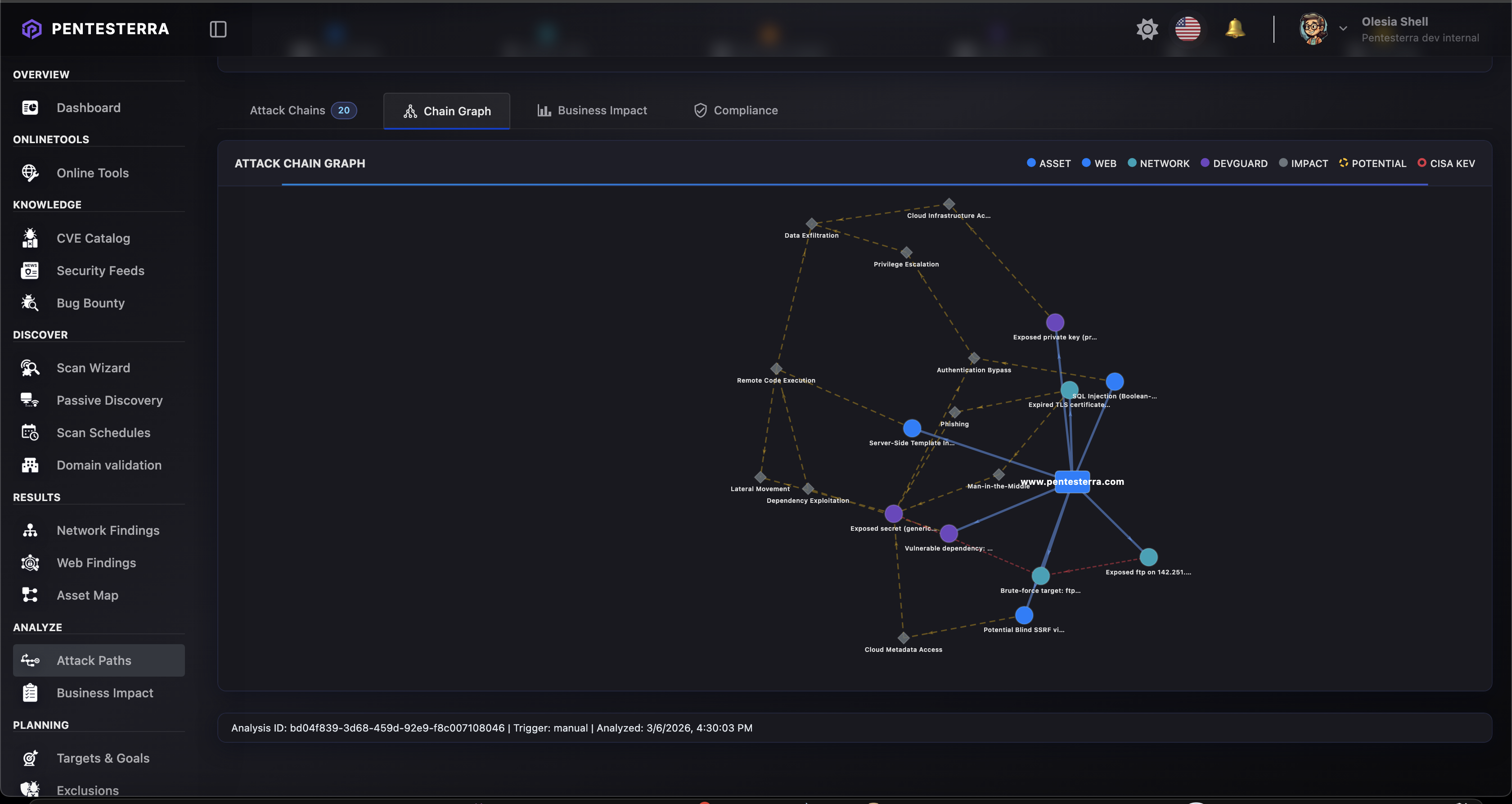
Screenshots
(screenshot placeholder)
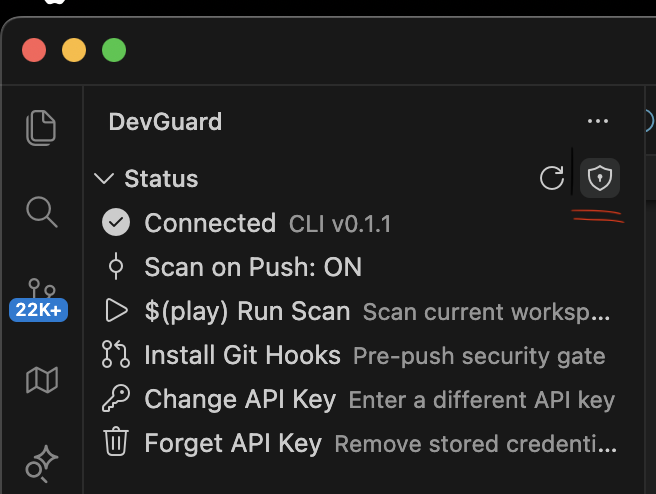
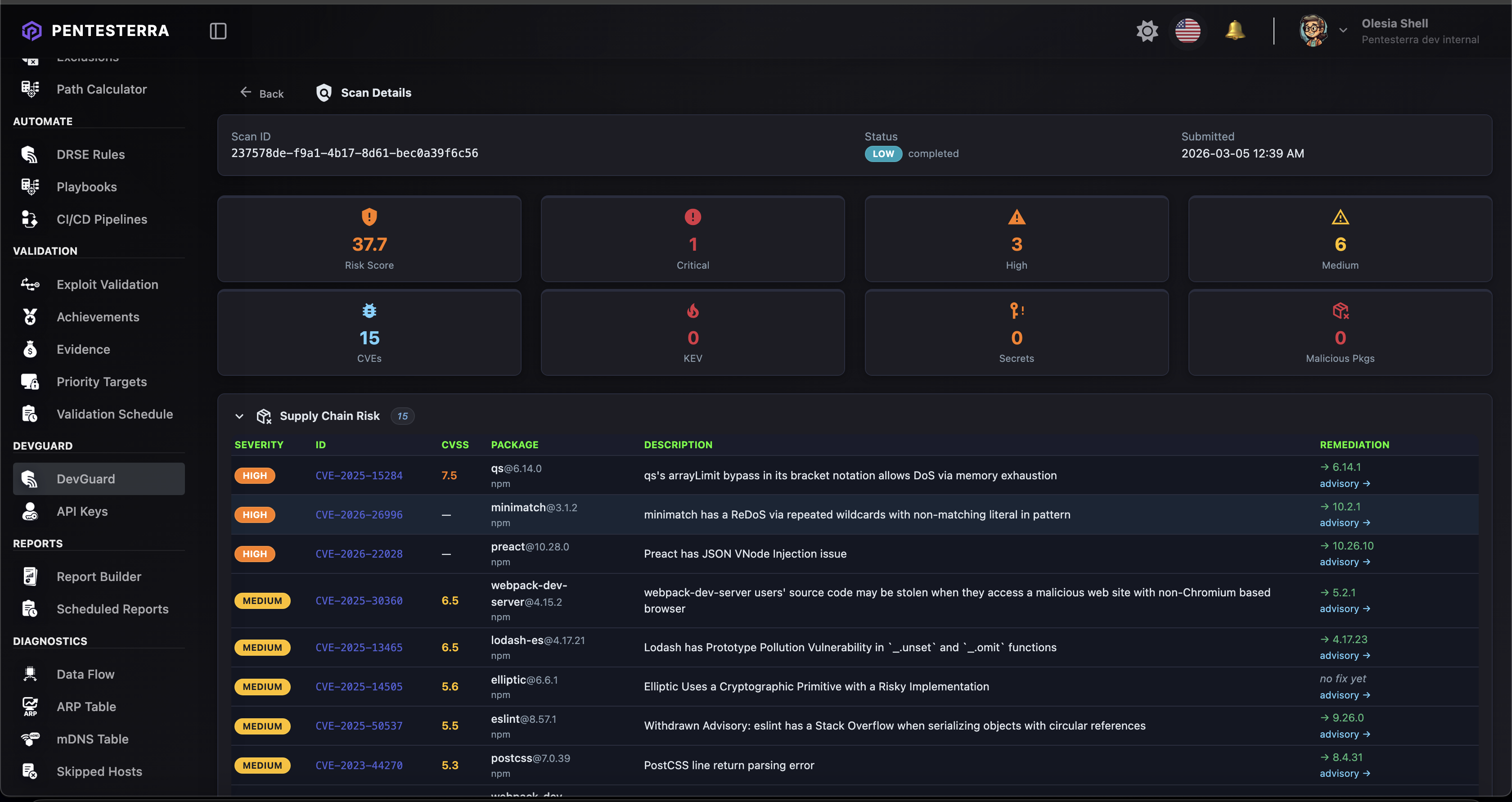
Scan Results
(screenshot placeholder)
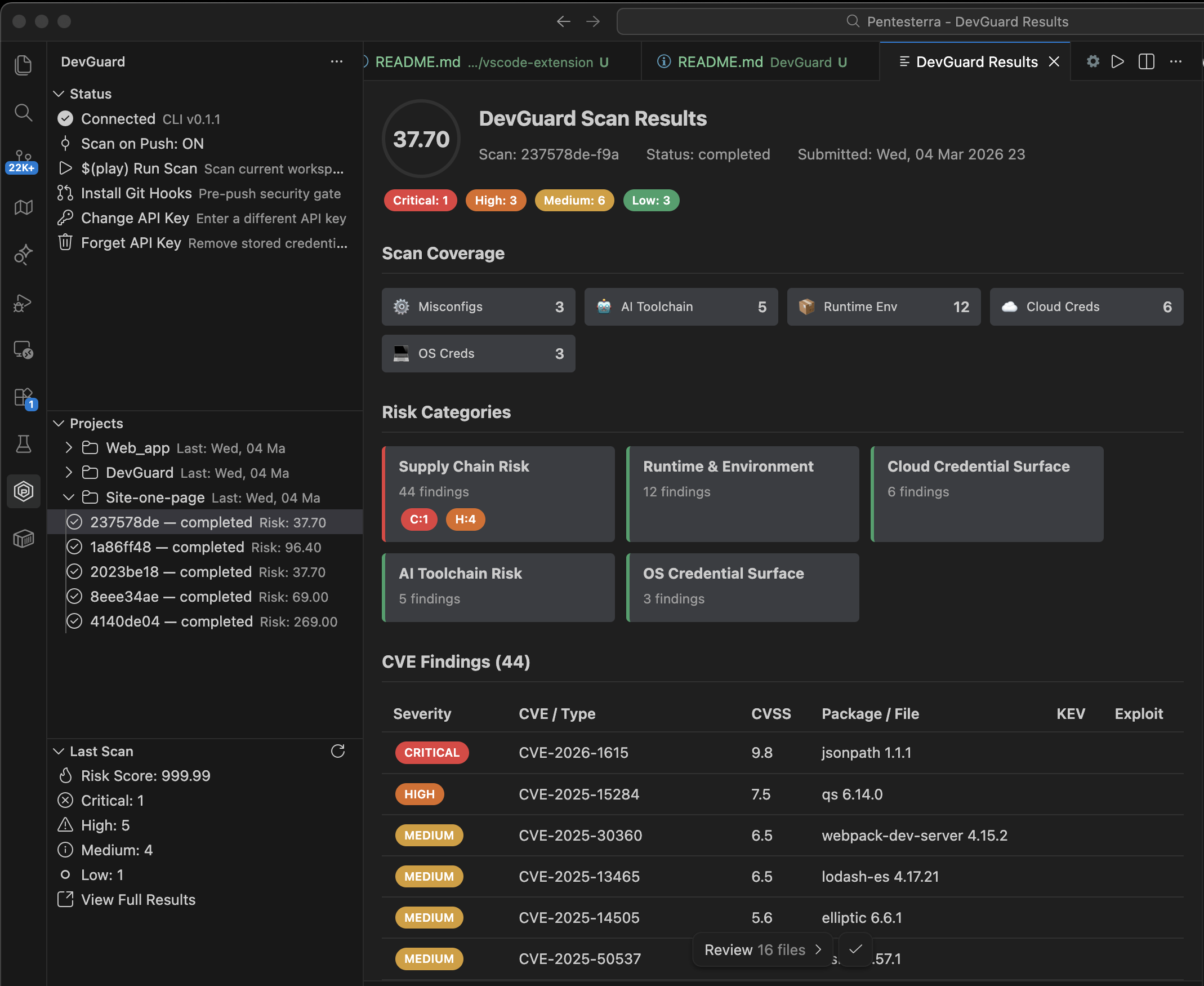
Api Key Configuration
(screenshot placeholder)
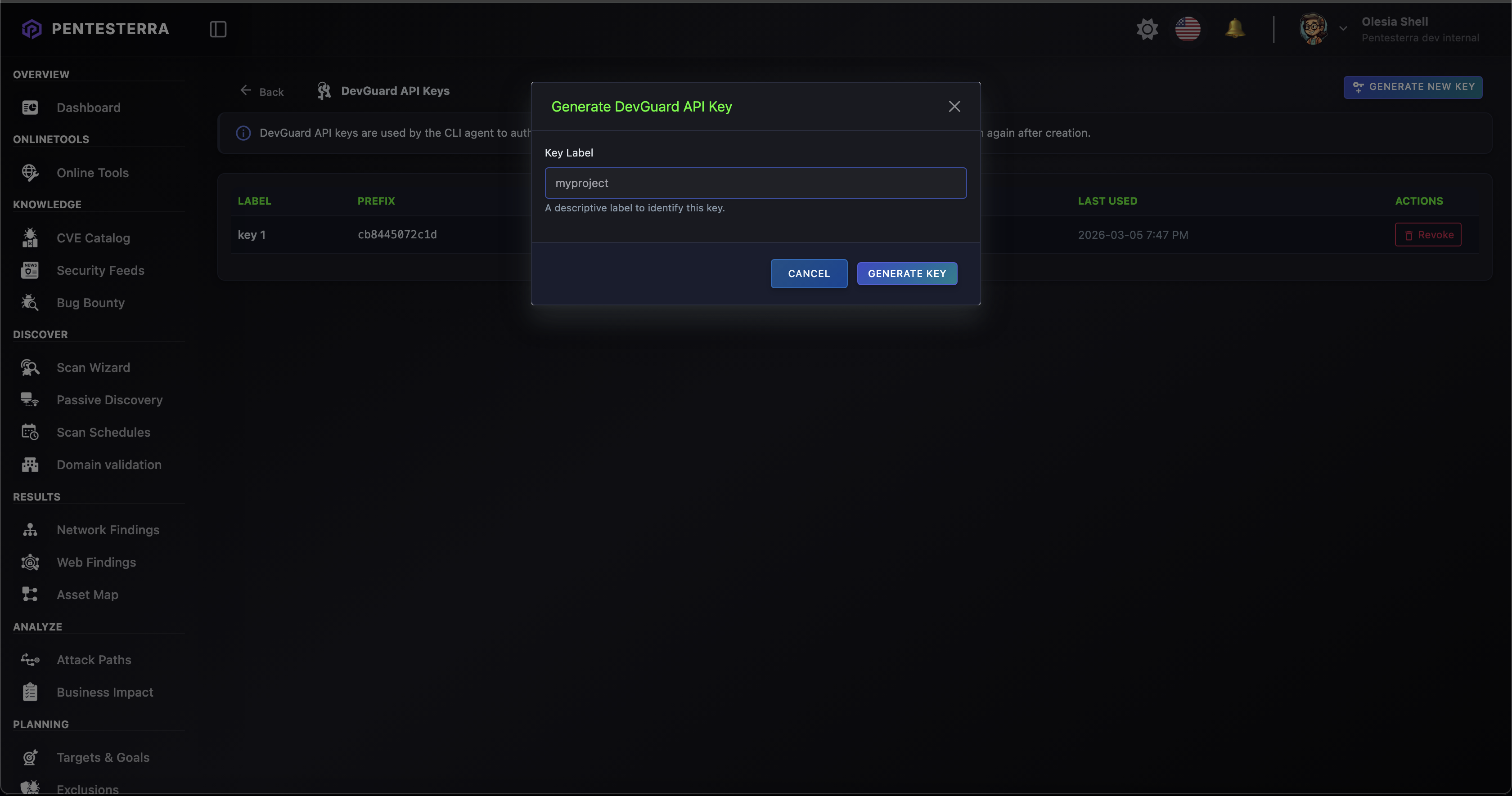
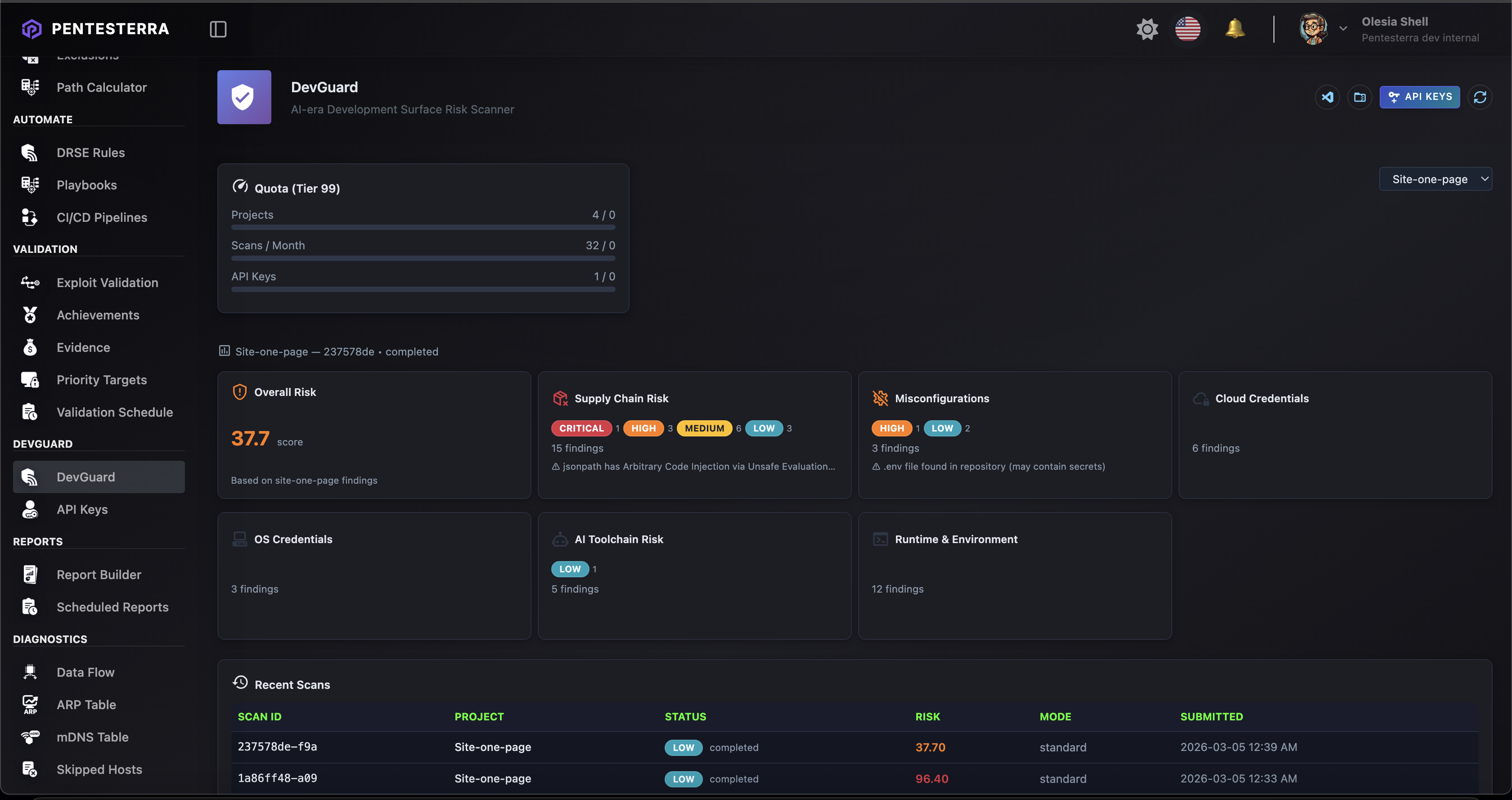
Scan Results on Web App
(screenshot placeholder)
Attack Chain Analysis
(screenshot placeholder)
Graceful Degradation
| Capability |
CLI + Key |
No CLI + Key |
No Key |
| Scan workspace |
✅ |
❌ |
❌ |
| Scan on push |
✅ |
❌ |
❌ |
| Install git hooks |
✅ |
❌ |
❌ |
| View results |
✅ |
✅ (HTTP) |
❌ |
| List projects |
✅ |
✅ (HTTP) |
❌ |
| View quota |
✅ |
✅ (HTTP) |
❌ |
Usage Tiers & Quotas
DevGuard capabilities depend on your Pentesterra account tier and available quotas.
| Capability |
Free Tier |
Developer Security |
Extended Dev Security |
Enterprise |
| Workspace scan |
✅ |
✅ |
✅ |
✅ |
| Dependency analysis |
✅ |
✅ |
✅ |
✅ |
| Secrets metadata detection |
✅ |
✅ |
✅ |
✅ |
| Pre-push security gate |
✅ |
✅ |
✅ |
✅ |
| Deep scan mode |
— |
✅ |
✅ |
✅ |
| Extended risk categories |
— |
— |
✅ |
✅ |
| Advanced analysis engine |
— |
— |
✅ |
✅ |
| Enterprise integrations |
— |
— |
— |
✅ |
Full plan comparison and current limits:
https://pentesterra.com/pricing
Commands
| Command |
Description |
DevGuard: Configure API Key |
Set your API key |
DevGuard: Scan Workspace |
Run a security scan |
DevGuard: View Last Results |
Open results webview |
DevGuard: Analyze Attack Vectors |
Generate attack vectors analysis |
DevGuard: List Projects |
Show projects in sidebar |
DevGuard: View Quota |
Show quota usage |
DevGuard: Toggle Scan on Push |
Enable or disable auto-scan |
DevGuard: Install Git Hooks (Pre-Push Gate) |
Install pre-push hook |
DevGuard: Uninstall Git Hooks |
Remove git hook |
DevGuard: Forget API Key |
Remove stored credentials |
DevGuard: Install CLI |
Install Python CLI |
DevGuard: Open Web Dashboard |
Open Pentesterra dashboard |
Settings
| Setting |
Default |
Description |
devguard.apiUrl |
https://api.pentesterra.com |
API endpoint |
devguard.cliPath |
auto |
Path to CLI binary |
devguard.scanOnPush |
true |
Enable post-push scan |
devguard.scanMode |
standard |
Scan mode (standard or deep) |
Security Model
DevGuard never uploads source code.
Only metadata may be transmitted:
- dependency names and versions
- lockfile metadata
- configuration signals
- environment metadata
Secrets and credentials are never transmitted.
All analysis runs inside the Pentesterra knowledge base and advisory engine.
Architecture
Extension (TypeScript)
↓
CLI subprocess (Python)
↓
Pentesterra API
↓
Security analysis + knowledge base
The extension acts as an orchestration layer.
All heavy analysis runs in the CLI and Pentesterra backend.
Build from Source
cd DevGuard/vscode-extension
npm install
npm run build
npm run package
Produces:
pentesterra-devguard-X.Y.Z.vsix
License
Copyright © 2024–2026 Pentesterra.
This software is proprietary and confidential.
Unauthorized copying, distribution, or use is strictly prohibited.