Micro Focus FortifyBuild better code and secure your software. Use the Micro Focus Fortify Azure DevOps build tasks in your continuous integration builds to identify vulnerabilities in your source code. Fortify Static Code Analyzer is the most comprehensive set of software security analyzers that search for violations of security-specific coding rules and guidelines in a variety of languages. The Fortify Static Code Analyzer language technology provides rich data that enables the analyzers to pinpoint and prioritize violations so that fixes are fast and accurate. Fortify Static Code Analyzer produces analysis information that helps you deliver more secure software, and makes security code reviews more efficient, consistent, and complete. Its design allows you to quickly incorporate new third-party and customer-specific security rules. Fortify on Demand delivers application security as a service, providing customers with the security testing, vulnerability management, expertise, and support needed to easily create, supplement, and expand a Software Security Assurance program. Fortify on Demand static assessments consist of a Fortify Static Code Analyzer scan performed and audited by our team of security experts. Fortify on Demand dynamic assessments mimic real-world hacking techniques and attacks using both automated and manual techniques to provide comprehensive analysis of complex Web applications and services. Featuring Fortify WebInspect for automated dynamic scanning, Fortify on Demand provides a full-service experience, complete with macro creation for authentication and a full audit of results by our experts to remove false positives and improve overall quality. Learn more about Fortify on Demand Micro Focus Fortify Azure DevOps build tasksUse the Fortify Azure DevOps build tasks in your continuous integration builds to identify security issues in your source code.
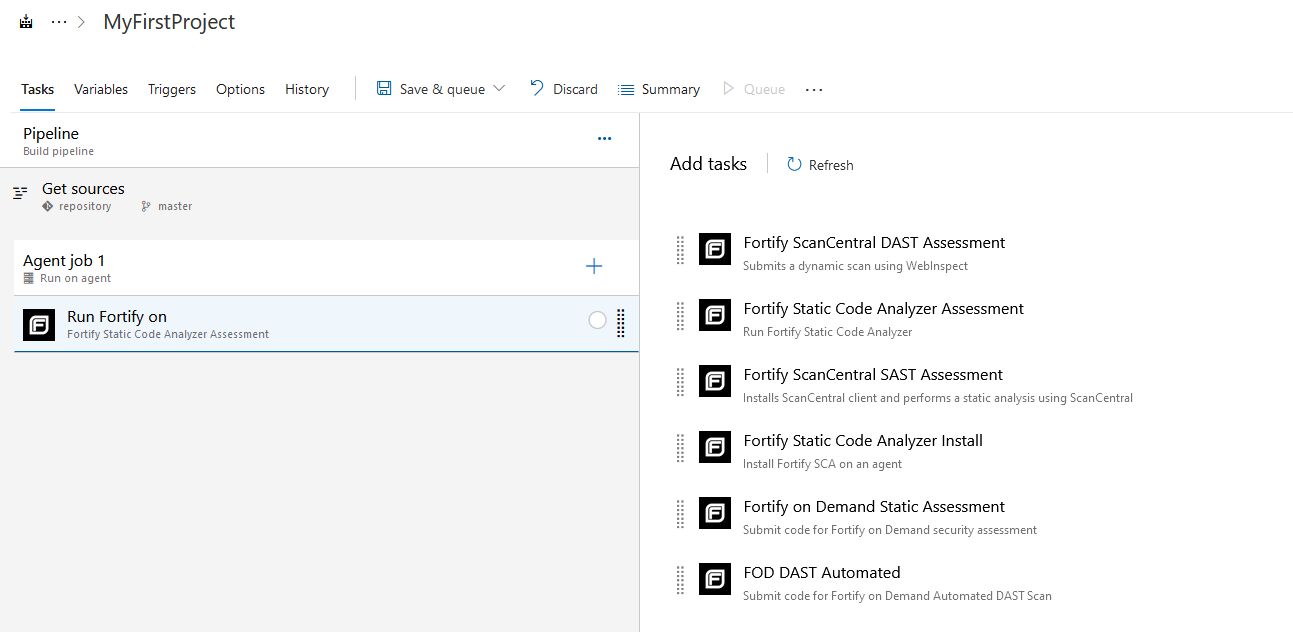
Fortify Static Code Analyzer InstallationThe Fortify Static Code Analyzer Installation task automatically installs and configures Fortify Static Code Analyzer. Users are required to prepare the Azure DevOps agent, which will run the Fortify Static Code Analyzer scan task with any dependencies needed to successfully build their software. Fortify Static Code Analyzer AssessmentThe Fortify Static Code Analyzer Assessment task enables you to run Fortify Static Code Analyzer as a build step and passes all parameters required to perform a scan. After the scan is complete, the scan results are available as a Fortify Project Results (FPR) file. The FPR and log files can be published as build artifacts. To review the scan results, download this artifact and open it in either Fortify Audit Workbench (AWB) or Fortify Software Security Center. You can also configure the task to upload the FPR to an existing Fortify Software Security Center server for enterprise vulnerability management. Fortify ScanCentral SAST AssessmentThe Fortify ScanCentral SAST Assessment task automatically submits a static scan request to Fortify ScanCentral SAST as a build step. The task will automatically install the Fortify ScanCentral client if not already installed. You can also upload your results to Fortify Software Security Center. After the scan is complete, you can view the results locally in Fortify Audit Workbench or in Fortify Software Security Center. Fortify ScanCentral DAST AssessmentThe Fortify ScanCentral DAST Assessment task automatically submits a dynamic scan request to Fortify ScanCentral DAST as a build step. After the scan is complete, you can view the results in Fortify Software Security Center. Fortify on Demand Static AssessmentThe Fortify on Demand Static Assessment task automatically submits a static scan request and uploads code to Fortify on Demand as a build step. Users can define scan settings, including scan and audit preferences, open-source component analysis, and specify third-party libraries to include. Once the scan is completed, results are made available through the Fortify on Demand portal and users are notified based on their subscription settings. FOD DAST AutomatedThe FOD DAST Automated task automatically submits an automated dynamic scan request to Fortify on Demand as a build step. The scan results are available in Fortify on Demand. For instructions on how to configure the Micro Focus Fortify Azure DevOps extension tasks into your build, see https://www.microfocus.com/documentation/fortify-azure-devops-extension |